Ethical Hacking - Process-ethicalhackerorg.tk
Like all good projects, ethical hacking also has a set of different steps. It helps hackers to attack a structured ethical hacking.
Metering
Reconition is the stage where the attacker collects information about the target using active or passive means. The widely used tools in this process are NMAP, Hopping, Maltago and Google Dork.
Scanning
In this process, the attacker starts actively investigating the target machine or network for those weaknesses which can be exploited. The tools used in this process are NESUS, NEXPSOZ and NMAP.
Get access
In this process, the vulnerability is located and you try to exploit it to enter the system. The primary device to be used in this process is Metasplight.
Maintain access
This is the process where the hacker has already acquired access to a system. After access, the hacker installs some backdoors to enter the system when it requires access to this proprietary system in the future. Metasploit is the preferred tool in this process.
Clearing track
This process is actually an immoral activity. It is to do with the removal of logs of all the activities that occur during the hacking process.
Reporting
Reporting is the last step to end the Ethical Hacking process. Here the Ethical Hacker compiles a report with its findings and work such as the tools used, the success rate, the identities of the weaknesses, and the process of exploitation.
Quick advice
Processes are not standard. You can adopt a set of different procedures and tools according to your techniques, with whom you are comfortable. As long as you are able to achieve the desired results, the process is of least importance.
Ethical Hacking - Process
Various safety training manuals explain the process of ethical hacking in various ways, but for me as a certified Ethical Hacker, the entire process can be classified in the following six steps.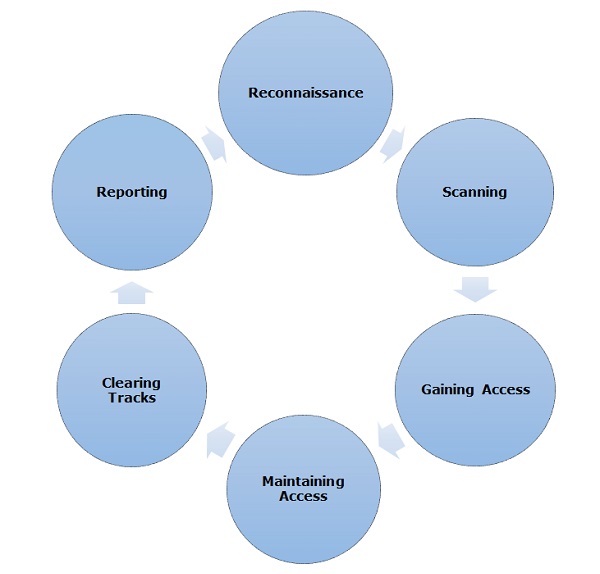 |
| Ethical Hacker org |
Metering
Reconition is the stage where the attacker collects information about the target using active or passive means. The widely used tools in this process are NMAP, Hopping, Maltago and Google Dork.
Scanning
In this process, the attacker starts actively investigating the target machine or network for those weaknesses which can be exploited. The tools used in this process are NESUS, NEXPSOZ and NMAP.
Get access
In this process, the vulnerability is located and you try to exploit it to enter the system. The primary device to be used in this process is Metasplight.
Maintain access
This is the process where the hacker has already acquired access to a system. After access, the hacker installs some backdoors to enter the system when it requires access to this proprietary system in the future. Metasploit is the preferred tool in this process.
Clearing track
This process is actually an immoral activity. It is to do with the removal of logs of all the activities that occur during the hacking process.
Reporting
Reporting is the last step to end the Ethical Hacking process. Here the Ethical Hacker compiles a report with its findings and work such as the tools used, the success rate, the identities of the weaknesses, and the process of exploitation.
Quick advice
Processes are not standard. You can adopt a set of different procedures and tools according to your techniques, with whom you are comfortable. As long as you are able to achieve the desired results, the process is of least importance.



Post a Comment