Ethical Hacking 2019 - Wireless Hacking-ethicalhackerorg.tk
Ethical Hacking 2019 - Wireless Hacking
A wireless network is a set of two or more devices connected to each other through radio waves within a limited space range. The devices in the wireless network have the freedom to be in motion, but in relation to the network and share the data with other devices in the network. The most important point is that they have spread so much that their installation cost is much cheaper and faster than the wire network.
Wireless networks are widely used and easy to install. They use IEEE 802.11 standards. Wireless router is the most important tool in wireless networks that connects users to the Internet.
Ethical Hacking 2019 - Wireless Hacking.
 |
| ethicalhackerorg.tk
In a wireless network, we have access points that are wireless range extensions that behave as logical switches.
Although the wireless networks provide great flexibility, they have security problems. A hacker network can go packets without any building where the network is located. As wireless networks communicate through radio waves, a hacker can easily sniff the network from nearby location.
Most attackers use network sniffing to find the SSID and hack the wireless network. When our wireless card is converted into sniffing mode, they are called monitor mode.
 |
Kismat
Kismet is a powerful tool for wireless sniffing which is found in black distribution. It can also be downloaded from its official webpage - https://www.kismetwireless.net/index.shtml
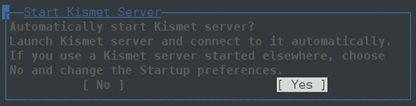
Let's see how it works. First of all, open a terminal and type the luck. Start the Kismet server as shown in the following screenshot and click Yes.
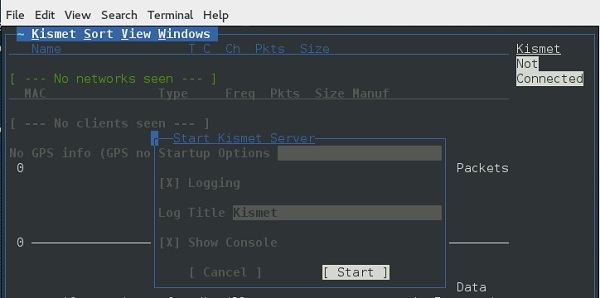
As shown here, click the Start button.
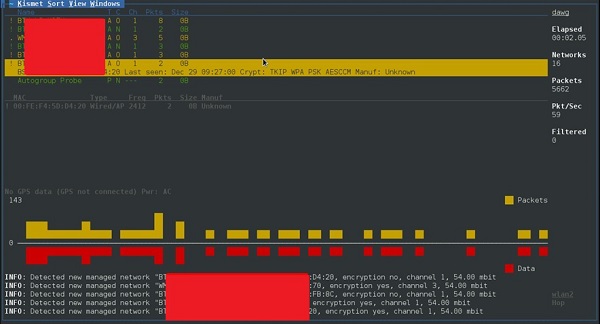
Now, kismet will start capturing the data. The following screenshots show how it will appear -
NetStumbler
NetStumbler is another tool for wireless hacking which is primarily for Windows systems. It can be downloaded from http://www.stumbler.net/
Using NetStumbler on your system is quite easy. You just have to click the scanning button and wait for the result, as shown in the following screenshot.
It should display screenshots as follows -
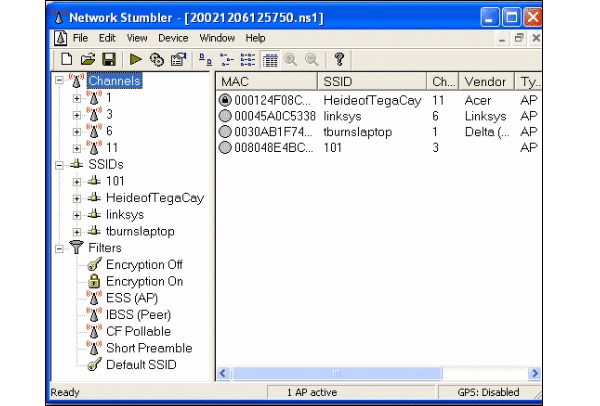
It is important to keep in mind that your card should support monitoring mode otherwise you will fail to monitor.
Wired Equivalent Privacy
Wired Equivalent Privacy (WEP) is a security protocol that was invented to keep the wireless network safe and keep it private. This data uses encryption on the link layer which refuses unauthorized access to the network.
The key is used to encrypt the packet before the transmission starts. An integrity investigation system checks that packets are not changing after transmission.
Note that WEP is not completely immune to security issues. It suffers from the following issues -
*CRC32 is not enough to ensure the complete cryptographic integrity of a packet.
*It is unsafe for dictionary attacks.
*WEP is also unsafe to deny services attacks.
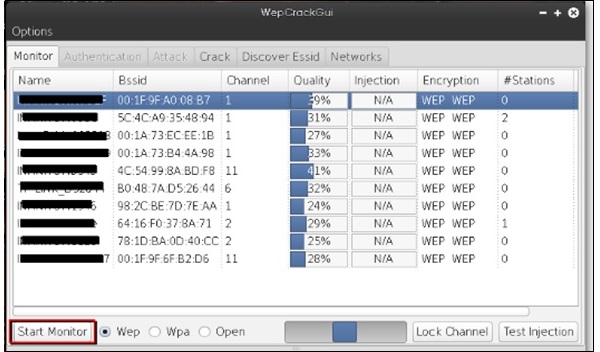
WEPcrack
WEPcrack WEP is a popular tool for cracking passwords. It can be downloaded from https://sourceforge.net/projects/wepcrack/
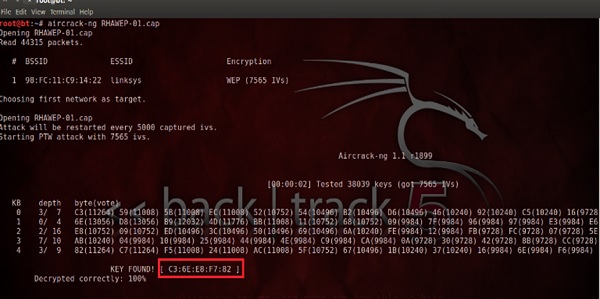
Aircrack-ng
Aircrack-ng is another popular tool to crack the WEP password. This can be found in the black distribution of Linux.
The following screenshots show how we sniffed a wireless network and collected packets and created a file RHAWEP-01.cap. Then we run it with the Aircrack-NG to decrypt cybercrip.
Wireless DoS Attacks
In the wireless environment, an attacker can attack a network from a distance and therefore, sometimes it is difficult to gather evidence against the attacker.
The first type of DoS is physical attack. This type of attack is very basic and it is based on radio interference that can be made from cordless phones which works in the 2.4 Hz range.
Another type is Network DoS Attack. As the wireless access point creates a shared medium, it offers the possibility of disrupting the traffic of this medium toward AP, which will slow down its processing towards those customers who try to connect. Such attacks can be made only by a ping flooding DoS attack.
Pyloris is a popular DoS tool that you can download - https://sourceforge.net/projects/pyloris/
Low Orbit ion Cannon (LOIC) is another popular tool for DoS attacks.

Quick tips
To secure the wireless network, you should keep the following points in mind -
*Change the SSID and network password regularly.
*Change the default password for access points.
*Do not use WEP encryption.
*Turn off guest networking.
*Update your wireless device's firmware.
*For more information, please follow this blog its free no charge or fee required*



Thanks alot brother If you want certification CEH-V10 at low price only18000/- for this course, Actually we our 3rd anniversery So we are offering everyone that BOOKS and TOOLs are free even practical online classes also free, only you have pay for Certification. And if you reffer anyone then your fee will be 15000/-.
ReplyDelete